What's new: Observatory now fingerprints the third-party software packages running on your internet-facing assets, and your vendors', without agents, source code, or pipeline access. CVEs that are mapped to software supply chain packages have been introduced.
Why it matters: AI-accelerated vulnerability discovery (Mythos and what follows) makes the software supply chain the highest-ROI target. SCA tells you what you intended to build; Observatory tells you what's actually exposed.
What to do: Existing customers, it's live in your tenant today. Everyone else, book a demo at acdsglobal.com.
On 7 April 2026, Anthropic announced Claude Mythos Preview, a model that autonomously identified a 17-year-old remote code execution vulnerability in FreeBSD and uncovered "thousands of high-severity vulnerabilities" across every major operating system and web browser. Shortly after the news of Mythos broke, Rob Joyce, former Chief of offensive hacking and later Head of Cybersecurity at NSA, said, “Every repository of code you rely upon just became a liability with a clock on it. Zero-day exploit development has gone exponential.”
Currently, access is restricted. A consortium of a handful of tech giants (called “Project Glasswing”) gets the keys. Everyone else waits for what comes next.
That "what comes next" is the point.
Zero-day vulnerability research - the often painstaking process of reviewing code to find obscure misconfigurations and errors, and unintended behaviour, is work that has required specialised skill and many weeks and months (or even years) of patient work, has just been industrialised and automated. Even if Mythos itself stays locked up, even if the model is half as powerful as the frenzied reporting suggests, the high-water mark has moved. Every major AI lab is now racing to ship models with increasing autonomous exploitation capability. Defenders are already facing attackers armed with AI tooling, and this trend is only going to increase in the coming months. This generation of frontier AI models will soon enable cyber criminals to find and weaponise vulnerabilities faster than most organisations can find and patch.
When vulnerability discovery becomes cheap, attackers stop hitting the hardest targets. They hit the ones with the biggest blast radius, the biggest return on investment. That is the software supply chain.
What is your software supply chain?
Why the supply chain is the Mythos-era target
Attacks on the software supply chain aren't new, but they have surged over the past five years and in the age of Mythos capabilities, is about to go exponential. Here is how the system works and why it is so vulnerable:
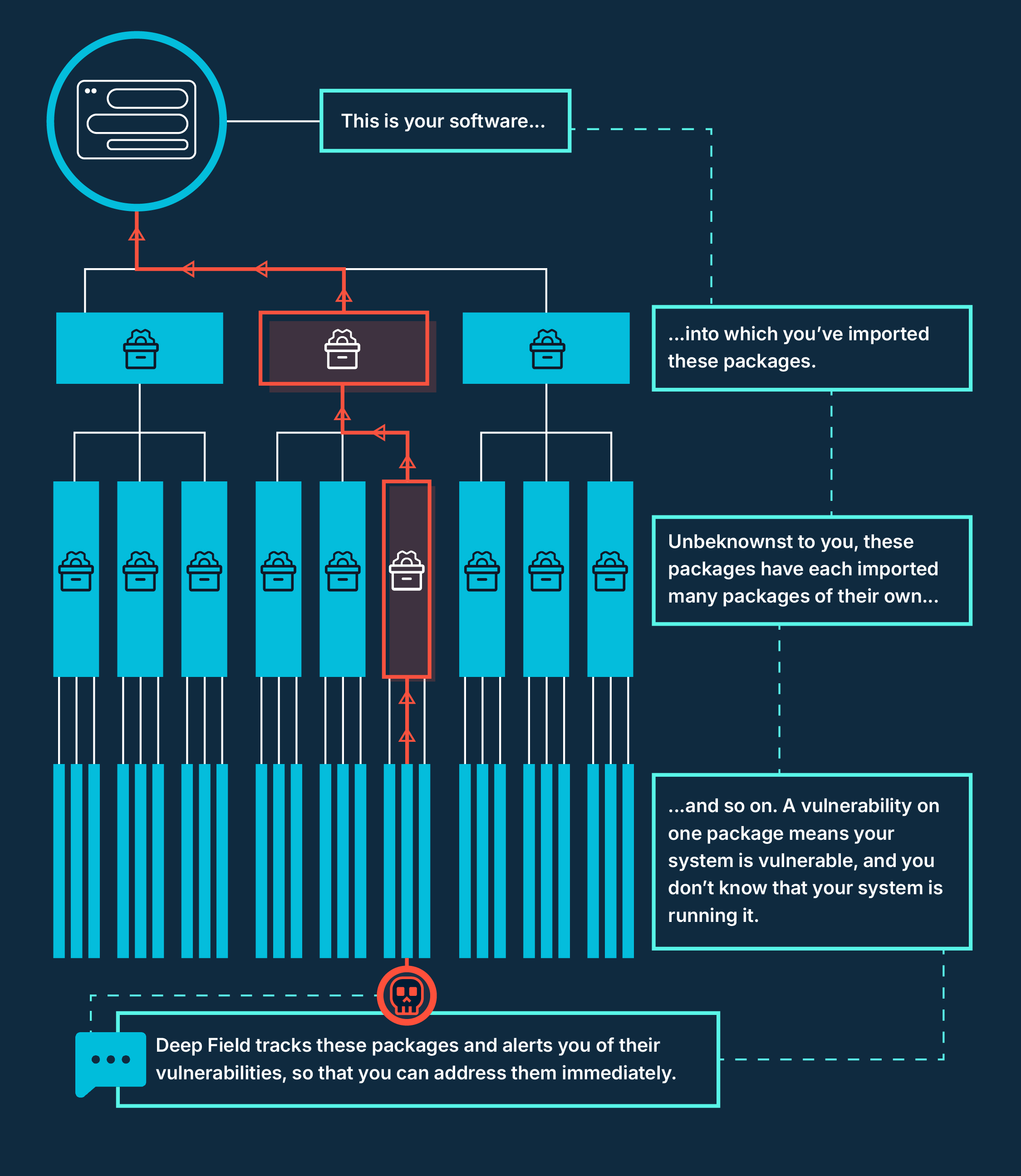
The Supply Chain: Modern software is built on a complex web of shared code. Developers rely on open-source packages, which in turn rely on other packages. This deep network of dependencies is the "software supply chain."
The Domino Effect: Because countless applications share these same foundational building blocks, a single compromised package can impact millions of deployments overnight.
The Entry Point: Hijacking just one software maintainer's account gives an attacker a direct backdoor into every customer using that code.
This pattern of widespread attacks is already accelerating:
- December 2025 — the JavaScript React vulnerability and quick weaponisation. Customers and partners reported thousands of engineering hours spent manually identifying which of their assets were affected.
- March 2026 — Axios compromised. 70 million weekly downloads exposed. One enterprise mobilised 8,000 developers overnight just to answer the question "are we running it?"
- 2025 totals — 297 supply chain attacks, up from 154 in 2024. A 93% year-on-year increase (Cyble). Projected global losses reach $138 billion by 2031 (Cybersecurity Ventures).
Now add AI-accelerated vulnerability discovery to that curve: finding new vulnerabilities will soon become trivial, which means defenders need to match the pace of detection. Organisations must greatly increase the observability of their software supply chain risks.
The gap no one has filled
Software Composition Analysis (SCA) tools sit in the development pipeline. They tell you what your engineers intended to build. They cannot tell you what you actually deployed, or what your vendors deployed, or what an attacker would see from the outside. We detect scripts in your web apps when they execute, so you can see what is actually being served to users.
External Attack Surface Management (EASM) platforms see your internet-facing assets. Until now, none of them have seen the packages running inside those assets. That gap is where the next generation of attacks will live.
“The value we gain from this functionality is unique; it is not provided by any other attack surface management tool that we use”.
Global Financial Services Institution - Apr 26
What we have just shipped
Today, we are releasing Deep Field Analytics as part of Observatory. We provide runtime vulnerability detection from our active supply chain monitoring. It identifies the specific software packages running on your websites and web applications, without the need for installing software on your developer machines, without the need for source code access, without pipeline integration. It then automatically maps each one to known CVEs and early-stage vulnerabilities before they’ve been assigned a CVE ID.
In short: the live, dynamic, near real-time Software Bill of Materials you never had to build.
Inside the capability
Package-level detection. Observatory's models have been trained on trillions of internet events from our telemetry, over 20 Billion events daily, enabling us and our agentic scanning to identify with over 99% accuracy the specific third-party packages running on each internet-facing asset, down to version level. No software on your dev machines. No source code access. No pipeline integration. Attackers don't need any of those things to find your packages, and neither should your defenders.
Automatic CVE and GHSA mapping. Every detected package is mapped to its known vulnerabilities and enriched with severity (CVSS), exploitability and exploit likelihood (EPSS), and CISA Known Exploited Vulnerabilities flags alongside other ID systems like Github Security Advisories (GHSA), which are increasingly important as NIST and CISA reduce staff responsible for CVE maintenance and enrichment. Because GHSA's are frequently self-published, they offer users earlier visibility of vulnerabilities. This means the information is available sooner than when an official CVE ID is assigned. Teams triage based on real-world exploitability, not severity scores alone, so the packages that attackers are actually weaponising rise to the top of the queue.
Transitive dependency visibility. The packages that cause the most damage are rarely the ones your developers chose directly, they are the indirect dependencies pulled in by other libraries, and increasingly by AI-assisted coding tools. Observatory surfaces those transitive dependencies in the same pipeline as everything else, closing the gap between "what we think we deployed" and "what is actually running."
Vendor software supply chain visibility. Extend the same detection to your vendors' internet-facing estates. See not just who is in your supply chain, but the specific packages running inside it. Shared exposure, the compromised package that sits in both your estate and a critical vendor's, is detected before it becomes an incident you inherit.
Continuous re-evaluation. Observatory does not stop scanning after the first sweep. As new CVEs and vulns are disclosed and new attacks emerge, your attack surface and your vendors' attack surfaces are automatically and continuously re-scored against them. Mythos-era vulnerability disclosure cadences will outpace manual review cycles—this capability is built for that reality.
What does this change mean for our customers?
- When a package is compromised publicly, Observatory tells you which of your assets are affected in hours or minutes, not weeks.
- The thousands of engineering hours for manual SBOM reconstruction that followed the React attack became a minutes-long scan.
- You can extend the same visibility to your vendors' internet-facing estates, detecting shared exposure before it becomes an incident for you.
- Secondary or Transitive dependencies, including those pulled in by AI-generated code, are flagged in the same pipeline as everything else.
Why now matters
Attacks have doubled in under a year. And on top of that curve, AI is now accelerating both sides of the equation, but it is accelerating the attacker's side faster. SBOM is becoming regulation, not best practice. The EU Cyber Resilience Act (enforcing December 2027), US Executive Order 14028, NIS2, and DORA all now require organisations to know what software is running across their own estate and their critical vendors. Observatory gives you that evidence externally, on demand, without waiting for a developer or a vendor questionnaire.
You cannot defend an attack surface you cannot see. In the Mythos era, "I'll know in two weeks" is not an answer your board will accept.
If you are an Observatory customer, the capability is already in your tenant. If you are not, now is the time to get signed up.
Observatory is ACDS's External Attack Surface Management platform, with Deep Field Analytics now in Beta for existing customers. Join the waitlist at acdsglobal.com.

